A Brief Comparison between Cybersecurity and IT Security
Share

Nowadays, businesses depend primarily on data to cater to their daily operation needs. This means you should make securing your company data one of your top priorities. When designing, a security policy for your company, make sure to include the physical assets, systems, and processes. Thankfully, there are multiple ways you can secure your business data.
The difference between Cybersecurity and IT Security
Securing the data from cybercriminals is one of the main factors that you should consider when designing a security policy. Similarly, offline tasks such as maintaining control of access to particular rooms, securing file cabinets with locks, and setting up guidelines for employees during daily operations are all significant steps you should take in order to secure your data. This separation in regards to securing your company data is what differentiates cybersecurity and IT security.
Note that while IT security involves all the processes that can secure all the systems and information from unauthorized access and use, cybersecurity focuses on safeguarding your data across the internet. In simple words, cybersecurity is limited to online elements and can be defined as a subset of IT security. Understanding the differences between these two security processes will help you avoid any loopholes when crafting a robust data security policy for your business.
What is Cybersecurity?
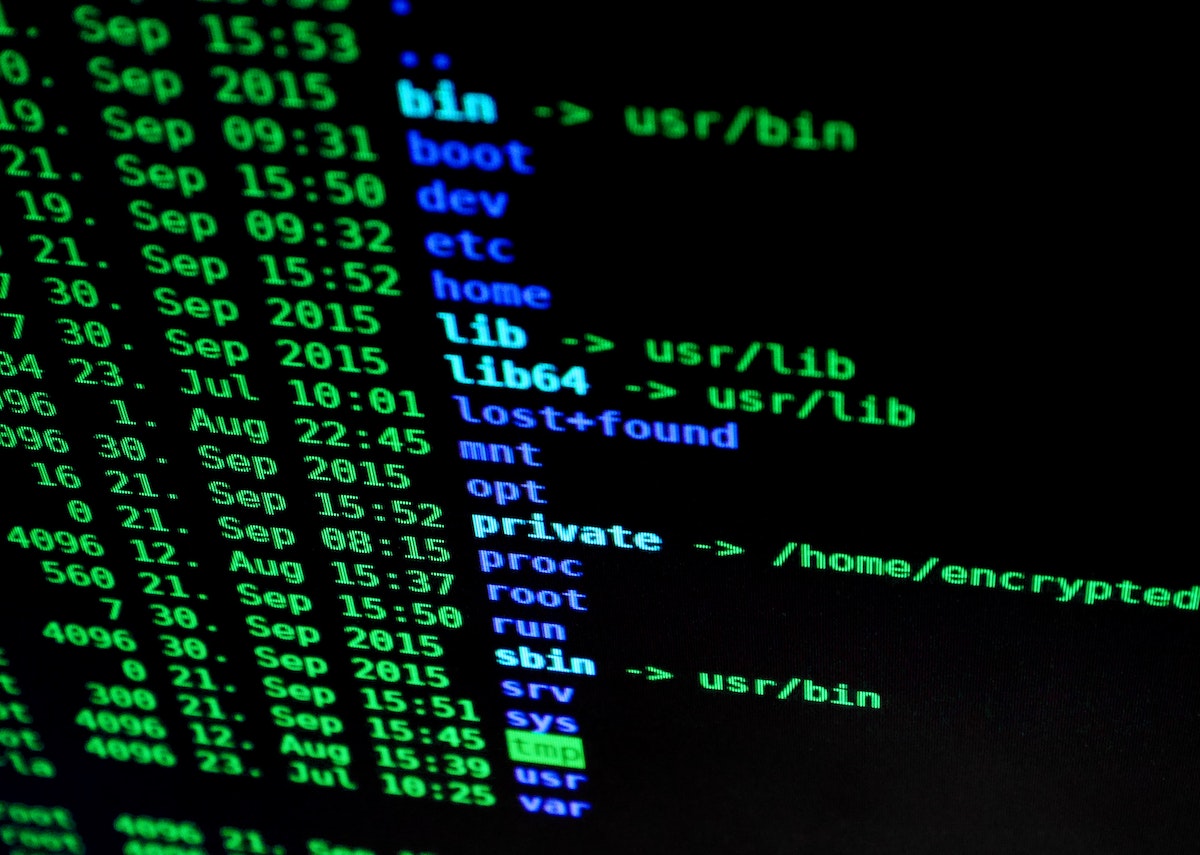
This process mainly focuses on securing your company data from online threats. Professionals employed in this field usually design and operate networks, servers, and software that can detect and tackle internet threats such as data loss, phishing, malware, etc. The number of hackers prying on company data is increasing everyday. Once they are able to break into your network system, all your confidential data will be stolen or damaged within seconds.
That being said, being their target is sure to put you at a great financial loss. On top of that, almost every business considers online channels to transfer data therefore making cybersecurity even more significant. This process includes multiple elements such as setting up firewalls to secure the data from malicious codes, monitoring the company network regularly for vulnerabilities, educating employees on cybersecurity and its significance, etc.
Usually, cybersecurity experts will be skilled in the latest hacking methods and will try to breach your security system regularly to find weak points as well as confirm that your security strategy is enough to withstand all such attacks. On a related note, the common methods used by professionals, in this case, are strong authentication methods to prevent hacking, encrypting sensitive data, and managing server accessibility.
What is IT security?
IT security is defined as the process of securing both the electronic and physical data from unauthorized access. This is actually a blanket term or larger approach that includes company policies, networks, information access, resource allocation, and data accuracy. Furthermore, when you hire a person to supervise your IT security department, make sure that he is capable of securing the file cabinets where confidential data are stored. At the same time, he/she must be able to manage firewalls on your machines to prevent phishing attacks.
Similarly, that individual will be responsible for securing the interconnected devices in your office as well such as printers, mobile apps, tablets, etc. An IT expert must also be able to monitor how the data is shared, the data policy is shaped, recency, accessibility, etc. Usually, IT professionals often recommend more resource allocation to handle the security data plan of the company as well as meet the business goals.
The relationship between cybersecurity and IT security
In a company, a cybersecurity expert and an IT professional must work hand in hand to prevent and respond to overall security issues. For instance, a hacker may break into your file cabinet room and leak details on the printed customer records or any other important information. Similarly, a cybercriminal may simply send a phishing email that makes your company’s system software vulnerable to malware attacks. Only the collective effort of cybersecurity personnel and IT experts will be able to tackle these issues.
In short, while most people tend to use these processes interchangeably, there are some major differences between both when it comes to the outcome, techniques, and scope, of these security plans. While IT security covers a wider area and applies to online elements, the cybersecurity is limited to the internet attacks, as mentioned earlier.
Likewise, you can find a huge difference between the approaches of both of these security management methods. Note that cybersecurity follows an approach of risk management. Conversely, IT security deals with daily data management and also depends on the company policy. Hence, every business must plan their IT security strategy when designing their core business proposal and even before the organization starts operating. Despite all the differences, both IT and cybersecurity are equally important and required for the security of your business data both offline and online.